Huawei MED-LX9 (Y6P 2020) Restoring OEM Info
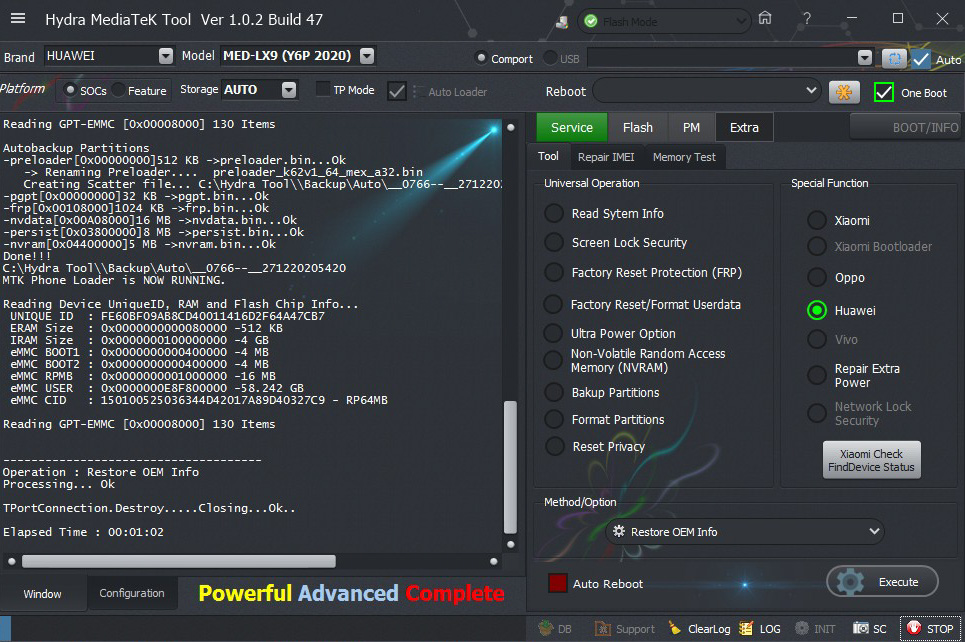
Screen Short:
Logs:
Logs:
Brand : HUAWEI Model : MED-LX9 (Y6P 2020) Connection : Flash Mode
=====================================
Connection
-Please wait...
-Connect Phone...
-Found...[COM4]
TPortConnection.Create...(COM4)..Opening...Ok
Handshaking...Ok
Identifying Hardware ID.....
BROM CPUID : 0766 (0000)MT6765[6765]
BROM HW_SW_VER : 8A00 CA00 0000 0000
FUSEID : 00000000
SECURE VERSION : 05
BL VERSION : FE
BR Secured : E5[SBC+SDA+SEL]
Security Authorization....
Sending[Huawei_Y6P_auth_sv5.auth] Accepted
Preparing Download Agent..
DA : MT6765_Huawei_MED.bin
Agent: MTK_DOWNLOAD_AGENT -HYDRA
Ver : MTK_AllInOne_DA_v3.3001.2018/10/18.17:38_452898
Init : Loader [1]
Sending : Accepted
Identifying Protocol...
Protocol : New
Synchronization...SYNC
Mode : brom
Preloader Initialization...
Parsing preloader_k62v1_64_mexico.bin
Init : Accepted
Execute Secondary Loader
Init : Loader [2]
Executing : SYNC
Reading Device UniqueID, RAM and Flash Chip Info...
UNIQUE ID : FE60BF09AB8CD40011416D2F64A47CB7
ERAM Size : 0x0000000000080000 -512 KB
IRAM Size : 0x0000000100000000 -4 GB
eMMC BOOT1 : 0x0000000000400000 -4 MB
eMMC BOOT2 : 0x0000000000400000 -4 MB
eMMC RPMB : 0x0000000001000000 -16 MB
eMMC USER : 0x0000000E8F800000 -58.242 GB
eMMC CID : 150100525036344D42017A89D40327C9 - RP64MB
DA Speed : high-speed
DA Speed : high-speed
Reading GPT-EMMC [0x00008000] 130 Items
Autobackup Partitions
-preloader[0x00000000]512 KB ->preloader.bin...Ok
-> Renaming Preloader.... preloader_k62v1_64_mex_a32.bin
Creating Scatter file... C:\Hydra Tool\\Backup\Auto\__0766--__271220203936\MT6765_Android_scatter.txt
-pgpt[0x00000000]32 KB ->pgpt.bin...Ok
-frp[0x00108000]1024 KB ->frp.bin...Ok
-nvdata[0x00A08000]16 MB ->nvdata.bin...Ok
-persist[0x03800000]8 MB ->persist.bin...Ok
-nvram[0x04400000]5 MB ->nvram.bin...Ok
Done!!!
C:\Hydra Tool\\Backup\Auto\__0766--__271220203936
MTK Phone Loader is NOW RUNNING.
Reading Device UniqueID, RAM and Flash Chip Info...
UNIQUE ID : FE60BF09AB8CD40011416D2F64A47CB7
ERAM Size : 0x0000000000080000 -512 KB
IRAM Size : 0x0000000100000000 -4 GB
eMMC BOOT1 : 0x0000000000400000 -4 MB
eMMC BOOT2 : 0x0000000000400000 -4 MB
eMMC RPMB : 0x0000000001000000 -16 MB
eMMC USER : 0x0000000E8F800000 -58.242 GB
eMMC CID : 150100525036344D42017A89D40327C9 - RP64MB
Reading GPT-EMMC [0x00008000] 130 Items
-------------------------------------
Operation : Restore OEM Info
Processing... Ok
TPortConnection.Destroy.....Closing...Ok..
Elapsed Time : 00:02:36
BR
Mount Everest


