Oppo F1s Plus Screen Pattern Lock successfully read by Hydra Tool
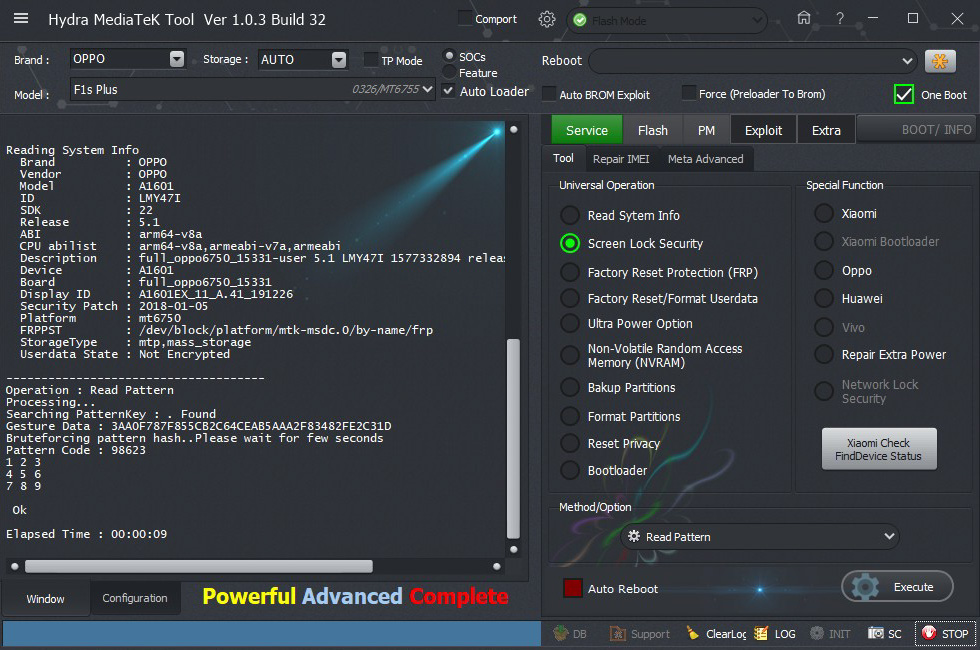
Screen Short:
Logs:
1. Run MTK Tool and choose "Sosc"
2. Choose Brand and Module as "Auto"
3. Go to "Service"--> "Tool" from Universal Option
4. Choose "Screen Lock Security"
5. Choose "Read Pattern" from "Method / Option" drop down menu.
6. Connect device to computer using USB Data Cable.
7. Wait until the operation is completed
2. Choose Brand and Module as "Auto"
3. Go to "Service"--> "Tool" from Universal Option
4. Choose "Screen Lock Security"
5. Choose "Read Pattern" from "Method / Option" drop down menu.
6. Connect device to computer using USB Data Cable.
7. Wait until the operation is completed
Screen Short:
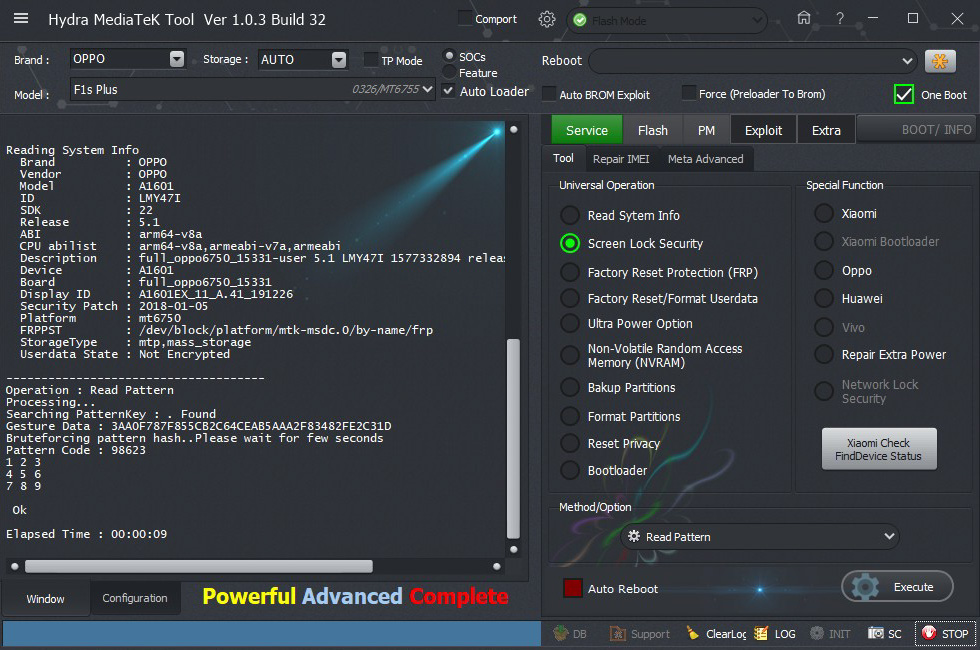
Logs:
BR=====================================
Searching for MTK Device...Found
Port Identification :DA_HIGHSPEED_VCOM
FriendlyName :MediaTek DA USB VCOM (Android) (COM34)
Device :6&1c75b1dc&0&1
SymbolicName :\??\USB#VID_0E8D&PID_2001#6&1c75b1dc&0&1#{a5dcbf10-6530-11d2-901f-00c04fb951ed}
Driver Ver :01/22/2015,3.0.1504.0
Reading Device UniqueID, RAM and Flash Chip Info...
UNIQUE ID : 89F6306A74E3B79A750527015D74D79C
ERAM Size : 0x0000000000040000 -256 KB
IRAM Size : 0x0000000080000000 -2 GB
eMMC BOOT1 : 0x0000000000400000 -4 MB
eMMC BOOT2 : 0x0000000000400000 -4 MB
eMMC RPMB : 0x0000000000400000 -4 MB
eMMC USER : 0x0000000747C00000 -29.121 GB
eMMC CID : 90014A484247346132A40A73092E8387 - HBG4a2
Reading GPT-EMMC [0x00008000] 130 Items
Reading System Info
Brand : OPPO
Vendor : OPPO
Model : A1601
ID : LMY47I
SDK : 22
Release : 5.1
ABI : arm64-v8a
CPU abilist : arm64-v8a,armeabi-v7a,armeabi
Description : full_oppo6750_15331-user 5.1 LMY47I 1577332894 release-keys
Device : A1601
Board : full_oppo6750_15331
Display ID : A1601EX_11_A.41_191226
Security Patch : 2018-01-05
Platform : mt6750
FRPPST : /dev/block/platform/mtk-msdc.0/by-name/frp
StorageType : mtp,mass_storage
Userdata State : Not Encrypted
-------------------------------------
Operation : Read Pattern
Processing...
Searching PatternKey : . Found
Gesture Data : 3AA0F787F855CB2C64CEAB5AAA2F83482FE2C31D
Bruteforcing pattern hash..Please wait for few seconds
Pattern Code : 98623
1 2 3
4 5 6
7 8 9
Ok
Elapsed Time : 00:00:09
Mount Everest


